Hrm, what to update on? My last post was released roughly 4 months ago. Who could have imagined where we would be today? Corona is … mostly a ploy to destroy the economy in the wake of the November elections. There are some real medical issues that could be present but its to the same group of people who are vulnerable to the seasonal flu. Its time to get back to work America.
Having addressed that … what else is there to talk about? Let me rummage about here. This is more of a scrap bin update so … things might be rough in places.
Projects
The biggest change is that I have a new shop. I would love to post pictures but operational security and all. The new shop gives me better capabilities. I’ve also expanded what tools I have on site. A basic stick/tig welder, lathe, and work bench are all welcome additions to my capabilities. I’m looking forward to starting my own business and maybe escaping from the nonsense that is corporate America. My sales site is already listed on here, but for kicks, check out my offerings at underthebedstudio.com.
I also built a painting cabinet that helps keep the fumes down in the house and give excellent finishes to parts I need to paint. One of the first projects that I used it for was a drive over antenna base. My intention to use this at the remaining service events this year that don’t get cancelled as a result of the Panicdemic.
Another cool project I worked on was a Cigar Punch. With my 3d printer I was able to iterate through designs pretty quickly. I threw out the iterations but took a picture first:
 Only took me 6 tries to get to the form factor I was happy with. I also finally found a pre-hardened material to make the punch itself from (drill bushings), which was the cause of Mk4 & Mk 4.1.
Only took me 6 tries to get to the form factor I was happy with. I also finally found a pre-hardened material to make the punch itself from (drill bushings), which was the cause of Mk4 & Mk 4.1.
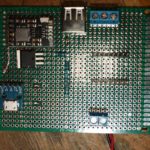
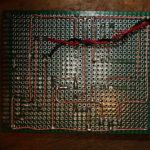
While I was looking at a few things, I ended up buying an ESP-12s which I found prebuilt firmware that would let me use it as a serial port over wifi. Pretty sweet. So here’s my interpretation of it:
Here’s the Schematic for the protoboard above. It uses an 18650 cell under the board for powering everything. And here is the STL for the carrier. I used standard 8-32 screws to hold the protoboard down. The charger circuit chip is here on Amazon.
Computer Jazz Hands
A few computer things that I’d like to talk about.
First up is the Retroflag GPi. This is a pretty slick little box that takes a Raspberry Pi Zero (Wireless if that’s your thing) and turns it into a self contained Retropie gaming machine. Being that its a Pi Zero, it struggles with anything over Super Nintendo but works pretty well for lots of other things. If you’re into gaming I highly recommend it. I just wish every single pi unit with the exception of the Pi3 wasn’t so damn finicky. I do have scripts that allow me to turn off the wifi and the bluetooth and also rsync over wireless. Code at the bottom. One thing I would recommend to everyone – just get a bluetooth keyboard at the same time. Normally I would recommend a 2.4ghz USB keyboard (I’m a fan of this one) but with the Pi Zero and the GPi case – bluetooth is best. I ended up with this one.
Ah, the Hak5 Jasager. They released the firmware 2.4 for the Mark V a month or so ago. I hate to say it, but I’ve never really gotten the thing to work as well as I would like. I’m always fighting with it, and it seems to be always corrupting sd cards – which kills my plugins. At this point, I would be hard pressed to buy the Mark VI. Hak5, thanks for all you’ve taught me. Best of wishes.
What about a Pwnagotchi? A wifi auth key hacking tomagotchi? Sweet. But my dislike of RasPi’s still applies. Also, its 2020 and now that I ponder the idea – I only see a couple of wifi configurations in the “wild.” The first is with a proper WPA2 password which can be tricky to catch and crack. The other is a captive portals with open associations. And no, fortune 500 employers and authentication portal doesn’t secure the traffic of the users. With open associations, no reason to associate. Just grab it from the air.
I built myself a FreeNAS box last year as well. This makes it super easy to back up my laptop across the network. A few recommendations
- Wire your network. Seriously. The speeds of a wired 10/100 easily exceed the speeds of wireless. While you’re at it, this is an excellent time to learn how to make your own network cables. Pick up a 100′ Cat5e cable and a crimpers + ends and go to town. Custom length cables make management much easier.
- Put in a “dumb” gigabit switch between your main computer and the freeNAS. I bought this one, but I couldn’t tell you if it would better then any other. Going to gigbit? Amazing. Most files get transferred before a status window can open. And backups – ironically 10 times faster.
- RAID. RAID all the things!
- And, do yourself a favor. Get a cheap UPS to put the freeNAS on so minor (or major) power outages let it fail gracefully.
- Having a well spec’d FreeNAS box lets you run servers all the time. I have one that starts up to handle my DNS requests. I’m running the Pi-Hole distribution because I’m not a fan of ads. Or the tracking nonsense that they do.
Getting a FreeNAS box set up was awesome. I highly recommend it. Right now, I’m loving everything about it.
I’m still running Fedora 30 on my laptop. I’ve never really booted to the Windows 10 installation that came with it – just to shrink the partition and I’m considering getting rid of it when I update to Fedora 32. I’ve held out against Fedora 31 long enough that I think I’m going to wait for 32 now. I usually do a fresh install. To many things can get muddled when doing an update and a fresh start it always nice. Probably make an image of the HD again before I wipe Windows 10 though. Shout out to Clonezilla. Thanks guys!
Miscellaneous Topics
Affiliate Links. There’s still no affiliate links here on the blog, and there will probably never, ever be unless the players change their tune. As I figured, they’ve started to weaponize the Terms of Service and its just not worth it for the little money. If the Youtube Adpocolypse can hit somebody like Demolition Ranch …. it will happen to anyone. Free Speech is important – don’t let yourself get caught in the trap. By the way, COVID-19 is totally Commie China’s fault.
Social Distancing. Ugh. Seriously? Why did it take this for people to realize that door knobs, pin pads, and people are nasty? They’re just nasty. And, stay the hell out of my face. COVID or not, I don’t want you within reach. Just back off. If you’re close enough that I could reach out and kick you … maybe you should back up just a touch.
Drones. I would love to get a TinyWhoop with FPV. I think it could be super useful and handy. But then I look at my other drones that I never touch and convince myself its to much. Drone guys, keep it up. I’ll have to live vicariously through your youtube videos.
Macro Lens. Why did I not buy one of these before? They are super awesome. I’ve messed with macro tubes, but they don’t work as well as a macro lense does. I highly recommend buying refurbished lenses and flashes directly from Canon. They’re a little more (like … $20) then what you would find for used prices, come with a warranty, and free shipping. I’ve always been super happy with Canon equipment and their repair shop. Seriously though, is this not gorgeous? Having a macro lense is great for documenting any of the fiddly things I do, like below. And honestly, I can see it being “one lense to rule them all” for me. The kit lens is a close second.
I recently went through an purged my youtube subscriptions. I think I got rid of half of them – many had been deleted or I no longer watched them. A few channels to shout out:
- Andrew Klavan – I love his satirical intros.
- Marling Baits – He makes fishing baits, and good videos just to have playing.
- This Old Tony – Dad Jokes and Machining.
- AVE – irreverant as f*ck.
- Ivan Miranda – massive scale 3d printing projects.
- Project Binky – in Colour! Dry british humor, and the only car show I’ve ever liked.
- Townsends – this man would have killed it on PBS when I was a kid.
The DS213 o-scope. Not a bad little device. Short on features, but for the price tag not a bad deal either. It let me see some things I couldn’t see with my multimeter. I have a proper oscope I need to repair, but to be honest I’m scared of the high voltage that’s inside. I found a drybox case online that holds this and the probes perfectly. Standard USB charging nonsense. 
While I’m at it, check on the NanoVNA. I’ve only really used it for checking SWR but there’s apparently a ton more that it can do. Here’s my kit, with the adapters I’ll need to get it to work with my equipment. As big as my go box and antenna setup is, its nice to know I can through this in my messenger bag or goruck with my laptop and be able to make some quick checks. This does standard usb charging as well but it wants a USB-C cable but doesn’t implement the fast charging spec. A waste.
Other Life Stuff
Still need to get digital working in my go box. Hopefully taking the time this week to put my HF rig on a dummy load and do the experimenting that I need to do.
I could really use a vacation. Somewhere tropical, sunny, and hot would be nice. Maybe via a cruise ship? Prices went through the floor now …..
Mentioning drones and how its not really something, I’d really love a Yaesu FT-818. Oh well, I probably wouldn’t use that either.
In Closing
Rock on folks. I’m going to peace out for a bit. Hope you enjoyed the randomness presented above.
RetroPie Scripts
Make a folder in the RetroPie roms directory called “bash” – mkdir -r ~/RetroPie/roms/bash
Copy over bash scripts. I have scripts for enabling and disabling the wifi adaptor, as well as using rsync across my LAN for rom directory syncing
Copy bash-mod/configs/bash into /opt/retropie/configs/
Copy over bash-mod/theme/bash into /etc/emulationstation/themes/carbon (or whatever theme you’re running is)
sudo /etc/emulationstation/es_systems.cfg and add the following code to the <systemlist> tree:
<system> <name>bash</name> <fullname>Bash Shell</fullname> <path>/home/pi/RetroPie/roms/bash</path> <extension>.sh .SH</extension> <command>/opt/retropie/supplementary/runcommand/runcommand.sh 0 _SYS_ bash %ROM%</command> <platform>bash</platform> <theme>bash</theme> </system>
Restart Emulation Station
bluetoothdown.sh
#!/bin/bash sudo rfkill block bluetooth
bluetooth-up.sh
#!/bin/bash sudo rfkill unblock bluetooth
wifi-down.sh
#!/bin/bash #sudo ifconfig wlan0 down sudo rfkill block wifi
wifi-up.sh
#!/bin/bash #sudo ifconfig wlan0 up sudo rfkill unblock wifi